(7) Assume val is an atomic integer in a Linux system. What is the value of val after the following operations have been completed? atomic set(&val, 10); atomic sub(8,&val); atomic inc(&val); atomic inc(&val); atomic add(6,&val); atomic sub(3,&val); Show your work (Clearly outline the results of the implementation of each statement)
Q: What is the Entropy reduction for this split? Show all calculations
A: The objective of the question is to calculate the entropy reduction for a given split in a dataset.…
Q: Say whether each of the following sets is regular (reg), context free but not regular (cf), or not…
A: a. {x ∈ {a, b, c, d}* | #a(x) = #b(x) = #c(x) = #d(x)}:This set represents strings in which the…
Q: 4. (8 pts) A communication link has a bit rate of 1 Gbps and a length of 40 km. Propagation velocity…
A: Effective bit rate refers to the throughput achieved after accounting for protocol overhead and…
Q: Part 2: Edit copy lab06.html, lab06.js and lab06.css to lab06.html, ab06.css, and lab06.js. In your…
A: In this question we need to create a web page with an input field and a button. When a user enters a…
Q: Why is the pipelined hash join not commonly used in a conventional DBMS? (A) It immediately produces…
A: The question is asking about the reasons why pipelined hash join is not commonly used in a…
Q: Alert dont submit AI generated answer. Please show the steps. 1.Convert (64DF)16 to octal. 2.Convert…
A: Approach to solving the question:(64DF)16 in octal is (62337)8(62337)8.(937)10(937)10 in BCD is…
Q: The module test2 contains a pandas DataFrame colors with a list of colors along with their…
A: Here are the detailed solutions for both tasks:The colors_extra table with the added 'grayscale'…
Q: Provide equations for A* and B* and construct a state table and complete the timing trace
A: Step 1: Step 2:Step 3: Step 4:
Q: Question pertaining to Arena Software.
A: To model the current system and the proposed alternative in Arena, we'll follow these steps:Define…
Q: Given the following State Transition Diagram, Complete the State Transition table.
A: Approach to solving the question:From the given state transition diagram, the following points are…
Q: Intellectual Property refers to creations of the mind, including inventions, designs, images etc.…
A: Introduction:Disaster Recovery as a Service (DRaaS) is a fundamental aspect of safeguarding…
Q: Consider the following CFG which is not in CNF: S→ AbC A → аA | Съ В → аАС CaBA Create a PDA for the…
A: A Pushdown Automaton (PDA) is a type of automaton that uses a stack to manage its computation. It is…
Q: Please help me create a cave class for a Hunt the Wumpus game. You can read the rules in it's…
A: In this question we have to write a Cave class which need to be designed for a "Hunt the Wumpus"…
Q: Question 3 a) Describe the greedy algorithm approach to solving an optimisation problem. Explain,…
A: a) Greedy Algorithm Approach to Optimization Problems The greedy algorithm is a simple and intuitive…
Q: For a Nim game with initial configuration [H1, H2, Hn] where the Hi values are all positive integers…
A: In Nim, the game starts with several heaps of objects, represented by positive integers. On each…
Q: Provide full C++ code for main.cpp, mystring.h and mystring.cpp Output should be: ----- Testing…
A: Step 1: 1)'main.cpp': #include <iostream> #include "mystring.h" int main() { std::cout…
Q: Which describes the Monge-Elkan similarity measure? Effective in matching names, since names are…
A: The Monge-Elkan similarity measure is a method used in computer science, specifically in the field…
Q: A Cougars Real Estate Inc. (CRE) sells houses. People who want to sell their houses sign a contract…
A: Use-Case Diagram: Class Diagram:```…
Q: Which is an example of an unstructured query? (A) SQL query over an XML database (B) XQuery query…
A: Let's break down each option:(A) SQL query over an XML database: SQL (Structured Query Language) is…
Q: As the CDO, how will you leverage data analytics? What will your goals for your analytical projects?…
A: Utilization of Data Analytics as a CDO: My role as Chief Data Officer would be to strategically…
Q: Intellectual Property refers to creations of the mind, including inventions, designs, images etc.…
A: Summative Report: Disaster Recovery as a Service (DRaaS) for INFRATEL Author: [Your Name], Risk…
Q: Method 2: Minimise the follow Boolean expression using Karnaugh Maps Y = ABC + ABC + ABC + ABC
A: If have any doubt feel free to ask.
Q: Write a java code for a concrete class called Circle based on the following specification: The…
A: The objective of the question is to create a concrete class in Java named 'Circle' with specific…
Q: Ex 3) Trace the following flowchart for when input values are -10, -1, 3, 2, 11, 13, 1, 0 and…
A: In this question we have to create a web application that allows users to input a series of numbers.…
Q: Given evolution of TCP's congestion window, provide following: a. List the times, at which TCP is in…
A: Solution:
Q: 4. Please show all work! Switched virtual circuit transmission overhead could be high to send a…
A: To calculate the minimum time to transmit one ATM cell from Miami to San Francisco on a basic SONET…
Q: Refer to image and provide detailed answers! Computer networks!
A: 1. Key Requirements for a routing function in Packet-Switching NetworksCorrectness ensures that the…
Q: 5. What happens if you map an aesthetic to something other than a variablename, like aes(color =…
A: Mapping an aesthetic, such as color, to an expression like `displ < 5` means that the color of…
Q: 8.18 Here are some type and variable declarations in C syntax: typedef char* Table1; typedef char*…
A: Structural Equivalence:Structural equivalence is based on the structure or layout of types or…
Q: What is the Entropy reduction for this split? Show all calculations
A: Detailed explanation:The goal is to calculate the entropy reduction when we split the dataset based…
Q: Alert dont submit AI generated answer.
A: 1. **Intercept**: The intercept represents the baseline log odds of the response variable when all…
Q: Please Provide Sources: What are the Biggest Cyber Threats for Financial Services in 2024? What are…
A: for more information ping me happy learning
Q: computer architucture(Draw the circuit of a 1-bit register that can perform the x+y.z: R. € I.…
A: Step 1:1-Bit Register with Conditional Addition and Retention (No PISO)While PISO (Parallel In…
Q: I need help the question
A: Let's go through the steps in detail. a. Construct the set of SLR items for the grammar:To construct…
Q: Consider the following two states representing board positions in the 8-queens problem. [3, 5, 4, 1,…
A: Let's analyze the potential resulting states:[3, 5, 4, 1, 1, 3, 8, 6]: This state is not valid…
Q: b, 1:11 b, 0:10 a, 1:01 a, 0:00 b, z; lz a, z; Oz b, 1; λ a, 0; z, z; z b, z; A b0;λ c, 1; 1 a, z; A…
A: Given is (q0,aacb,Z), Currently stack has Z as top.When we read the first alphabet a, 0 will be…
Q: Which of the following describes the operation of a positive edge-triggered D flip-flop? The input…
A: Step 1: Question 1)Answer : CThe output will follow the input on the leading edge of the clock…
Q: What is specified by a relational schema? (A) The number of arguments in a query B Limits of…
A: Within a database context, a relational schema may be thought of as a blueprint or plan that…
Q: ( aList. insert ( i, item ) ).remove (i) = aList
A: Here are in more detail you can read it if you still do not get why your Python code is wrong:: The…
Q: Please help me with these question. I am having trouble understanding what to do. Please use HTML,…
A: The objective of the question is to create a function that uses binary search to find a number in an…
Q: #include <stdio.h> #include <stdlib.h> #include <unistd.h> #include…
A: A): The return value of open() is explained perfectly. It clearly states that it returns a file…
Q: Could you do this, please? I really need help on this. in Java
A: The objective of the question is to create a Java program that simulates the movement of cars across…
Q: Hi there, could you kindly assist me with creating Turing machines for parts B and C? I'm finding it…
A: Sure! I'll provide you with the Turing machines for both parts (B and C) of the question. I'll…
Q: 2. Please write in complete sentences For a certain trap generated by an agent, it is desired to…
A: STEP BY STEP ANSWER:Answer:v1v2TrapForwardingTable or v2ManagerTableIf you are creating SNMPv1 or…
Q: Alert dont submit AI generated answer. Now you want to focus on the summarizing data for Account…
A: Formulas for Counting Account Reps and Calculating Total SalaryHere are the formulas you can use in…
Q: In C++, using on GLFW3 and glad.h, how do you implement a 3D Sphere in terms of implementation…
A: To implement a 3D sphere in C++ using GLFW3 and glad.h, you'll first need to create a vertex buffer…
Q: PYTHON/COMPUTATIONAL STOICHIOMETRY Make an organized output of the species and stoichiometric data…
A: import numpy as np reactions = [ "C(s) -> C(g)", "2 C(g) + O2 -> 2 CO", "CO + H2O…
Q: Write a program in C as follows:- Create an array of integers named “toy” that has 120 rows and 4…
A: The objective of the question is to create a C program that manages a toy bag. The program should be…
Q: Provide full C++ main.cpp, fraction.cpp, fraction.h
A: The code is provided below: //fraction.cpp #include <iostream> #include <fstream> using…
Q: The first problem is related to the variable n and its value. Explain what goes wrong. Provide a…
A: In the revised implementation of the function `count_crossings_and_nestings`, the variable `n`,…
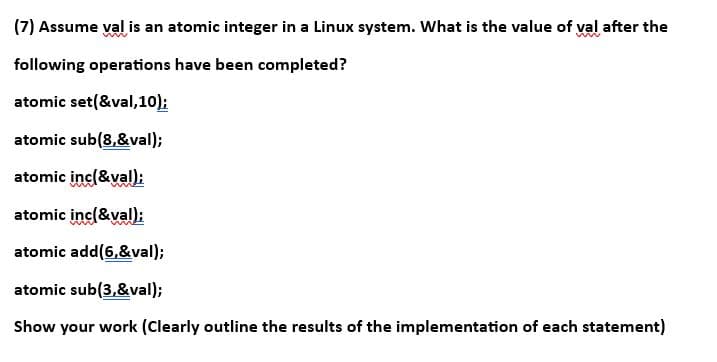
Please solve and show work. Thank you.
Assume val is an atomic integer in a Linux system. What is the value of val after the
following operations have been completed?
atomic set(&val,10);
atomic sub(8,&val);
atomic inc(&val);
atomic inc(&val);
atomic add(6,&val);
atomic sub(3,&val);
Show your work (Clearly outline the results of the implementation of each statement)
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- In the below stack allocation, what is the current value of top after execution of the following code (i.e. after the function using the second activation record)? Hint: remember that stacks grow from highest address toward lower address. StackAllocatr m = new StackAllocatr(5); m.push(1); m.push(2); m.popForking a new process in Linux is claimed to use a copy-on-write policy so that although the text heap and stack are the same for a parent and child before and after the fork they change as soon as a data item is written by either the parent or child. Write a small program that verifies whether this is true or notPlease write in C++ and run in linux. This assignment is about fork(), exec(), and wait() system calls, and commandline arguments. Write two C++ programs, to be named parent.cc and child.cc and compiled into executable parent and child, respectively that, when run, will work as follows: parent takes in a list of gender-name pairs from the commandline arguments creates as many child processes as there are in the gender-name pairs and passes to each child process a child number and a gender-name pair waits for all child processes to terminate outputs “All child processes terminated. Parent exits.” And terminates. child receives a child number and one gender-name pair arguments from parent outputs “Child # x, a boy (or girl), name xxxxxx.” Note: content of output depends on data received from parent Sample run To invoke the execution: >parent girl Nancy boy Mark boy Joseph parent process does the following: outputs “I have 3 children.” -- Note: the number 3…
- A reference parameter differs from an output parameter in that a reference parameter ______________________ but an output parameter does not. a. occupies a unique memory address b. must be a simple data type c. receives a memory address d. requires an initial valueI'm having a hard time seeing the problem with this buffer overflow problem can someone please elaborate if its secure or not, and if there are any other issues with the implementation in the problem? Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are there any other issues within the function's implementation below? Explain your reasoning. int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }For the following program, considering a() as call to fork(),during execution, show the number ofprocesses that will be spawned and number of times “Created” will be printed? Justify your answers.#include <stdio.h>#include <unistd.h>int main(){a();a() && a() || a();a();printf("Created\n");return 0;}
- Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why?why not? Are there any other issues within the function's implementation below? Please explain your reasoning. int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }When dealing with Linux, it provides a set of operations that ensure atomic operations on a variable, and these operations can be used to avoid basic race problems, so what happens when working with uniprocessor and multiprocessor systems?When using a C++ inclusion guard on a library interface file, why is it essential that the symbol or name used in the guard not be identical to any other uses of the symbol or name in the guard? Assuming that the symbol does not need to be unique and then showing what occurs when two libraries that are to be #included in the same application share the same symbol is an effective use of the proof by contradiction technique in this circumstance. Here, we have an actual application.
- How does this method cause memory leaks? How do I make it multi-thread safe? I have this JUnit test method that checks if my method is working. What it does is to. Inherit @Before and @After methods from BaseTest Since for every class, a session is created before, use it for ServiceTest.testUpdate() when we have to use session.save. ----------------------------------------------------------------------------------------------------------------------- public class BaseTest{ @Autowired protected SessionFactory sessionFactory; protected Session session; @Before public void createSession() { session = sessionFactory.openSession(); } @After public void closeSession(){ if (session != null) { session.flush(); session.close(); } } } public class ServiceTest extends BaseTest{ @Autowired private FoodService foodService; @Test public void testUpdate() { Food food= new Food("Japanese", "Ramen"); session.save(student); int id = (int) session.getIdentifier(student); session.flush();…Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are there any other issues within the function's implementation below? Explain your reasoning. int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }Is there a special reason why the symbol or name used in the C++ inclusion guard on a library interface file has to be special? A helpful tactic in this situation is to use proof by contradiction: assume that the symbol doesn't need to be unique, and then show what happens when two libraries that are both #included in the same application use the same symbol.

